
AI-driven defense is only as strong as the ground-truth data it relies on.
We believe that security automation and AI-driven defense are only as effective as the ground-truth intelligence they’re built on. ELLIO delivers foundational threat intelligence focused on the earliest phases of the attack lifecycle - reconnaissance and mass exploitation - where adversaries signal intent before impact. Our mission is simple: Reduce operational burden and security spend by disrupting threats upstream, before incidents escalate and become costly.
5 JAN
Stealth Launch
Started research and analysis of the pre-attack threat landscape.
30 JUN
High-signal IP Blocklist Release
Launched our flagship IP blocklist - ELLIO Threat List MAX - a large-scale, high-fidelity IP blocklist derived from observed exploitation and recon traffic in real-time.
1 OCT
Smart ELLIO Blocklist Manager
Launched a customizable platform for precise IP blocking and allowlisting, reducing false positives while maintaining strong protection.
1 APR
ELLIO Exploitation and Recon Threat Intelligence Platform
Launched a unified platform for actionable defense against mass exploitation and network reconnaissance, including threat intelligence, perimeter protection, and cyber deception.
1 NOV
Advanced Network Fingerprints
Added network fingerprinting analysis to the ELLIO Intelligence Platform, giving teams faster insights and early-stage attack prevention.
15 DEC
Tripled Sensor Coverage
Expanded ELLIO Cyber Deception Network threefold, improving real-time detection and visibility across threats.
1 JUN
MITRE ATT&CK® Integration
Integrated the MITRE ATT&CK® framework into the ELLIO Intelligence Platform for deeper threat analysis.
5 AUG
Open-Source TCP Fingerprint Firewall
Introduced Recon Shield, an open-source TCP fingerprint firewall, boosting protection against reconnaissance and pre-attack activity.
15 JAN
Interactive Historical IP Timeline
Expanded ELLIO Intelligence with a Historical IP Timeline for deeper insights, easier filtering, and quick report exports.
2022
5 JAN
Stealth Launch
Started research and analysis of the pre-attack threat landscape.
2023
30 JUN
High-signal IP Blocklist Release
Launched our flagship IP blocklist - ELLIO Threat List MAX - a large-scale, high-fidelity IP blocklist derived from observed exploitation and recon traffic in real-time.
1 OCT
Smart ELLIO Blocklist Manager
Launched a customizable platform for precise IP blocking and allowlisting, reducing false positives while maintaining strong protection.
2024
1 APR
ELLIO Exploitation and Recon Threat Intelligence Platform
Launched a unified platform for actionable defense against mass exploitation and network reconnaissance, including threat intelligence, perimeter protection, and cyber deception.
1 NOV
Advanced Network Fingerprints
Added network fingerprinting analysis to the ELLIO Intelligence Platform, giving teams faster insights and early-stage attack prevention.
15 DEC
Tripled Sensor Coverage
Expanded ELLIO Cyber Deception Network threefold, improving real-time detection and visibility across threats.
2025
1 JUN
MITRE ATT&CK® Integration
Integrated the MITRE ATT&CK® framework into the ELLIO Intelligence Platform for deeper threat analysis.
5 AUG
Open-Source TCP Fingerprint Firewall
Introduced Recon Shield, an open-source TCP fingerprint firewall, boosting protection against reconnaissance and pre-attack activity.
2026
15 JAN
Interactive Historical IP Timeline
Expanded ELLIO Intelligence with a Historical IP Timeline for deeper insights, easier filtering, and quick report exports.
European Cybersecurity for the earliest stage of attacks.
Based in Prague, where Karel Capek first coined the word “robot” in R.U.R., ELLIO confronts the modern evolution of automated attacks powered by bots and AI.
Today, those “robots” exist in a different form - they’re probing, scanning, and exploiting systems at scale across the internet. ELLIO detects these reconnaissance and mass exploitation campaigns at their earliest stage, enabling security teams to neutralize threats before they escalate into costly incidents.

AI-adaptive cyber deception.
ELLIO operates a global deception network and honeypots, giving you direct access to core threat data with unique context, free from third-party noise and data contamination. We continuously envolve cyber deception to capture authentic adversary behavior at scale.

Realistic attack surface emulation.
Coverage of early-stage attacks.
Behavioral and high-interaction capture.
Metadata ready for attribution.
Works with automated response systems.
Inspired by the legacy of the first antivirus pioneers.
ELLIO was founded by Vlad Iliushin and Jana Tom, who met at Avast (now Gen Digital Inc.), the company behind the first Windows 95 antivirus. Backed by Presto Ventures, they launched ELLIO to automate, optimize, and uncover emerging threats before they grow into incidents.


[watchdog]: Inside a Mirai variant with six-layer persistence
An open directory is serving a Mirai variant across 14 CPU architectures - all updated yesterday. It kills competitors by SHA256 hash, persists through six layers, and hides as a kernel thread. Here's what's inside.

What Gets Deployed via Exposed Docker APIs
Over 1,000 unique IPs scan for exposed Docker APIs every day. A fraction go further. We captured every container creation payload and classified them by monetization strategy.
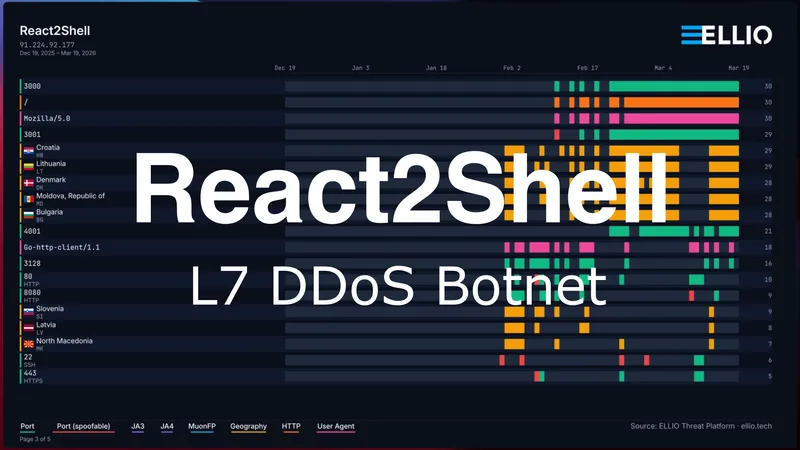
React2Shell Update: Custom Go L7 DDoS Botnet
A single delivery IP has been exploiting React2Shell to distribute malware from an open directory. 31 binaries including a custom Go L7 DDoS botnet with Cloudflare token forgery, two Mirai variants across 13 CPU architectures, and a C2 server.

Threat Intelligence Platforms by Use Case: 2026 Guide
Not all CTI platforms are built for the same purpose. Differences in data sourcing, architecture, and enrichment capabilities mean the “best” platform is defined by its fit for operational use cases, such as reducing SIEM noise, supporting threat hunting, or detecting fraud.


Internet Background Noise: The Hidden Cost Layer in Security Operations
The same layer that drives cost also carries early attack signals. With visibility into reconnaissance, teams separate signal from noise and stop attacks before they become operationally burdensome and costly.


ELLIO Founder Vlad Iliushin Hands AMTSO Leadership to Stefan Dumitrascu
ELLIO today announced that its founder, Vlad Iliushin, has completed his term as President of AMTSO (Anti-Malware Testing Standards Organization) and handed over the role to Stefan Dumitrascu, Founder and CEO of Artifact Security.
What is ELLIO?
ELLIO is a research-driven cybersecurity platform powered by its global cyber deception network. It delivers foundational threat intelligence focused on the earliest stages of attacks - mass exploitation and network reconnaissance. By providing real-time insights into malicious activity, ongoing reconnaissance, and exploitation campaigns, ELLIO helps organizations detect and stop threats before they escalate and become costly.
How is ELLIO different from other threat intelligence providers?
ELLIO specializes in reconnaissance and mass exploitation - the earliest stages of attacks. Powered by data from our own global cyber deception network, our intelligence is entirely proprietary with zero third-party contamination. Unlike traditional threat intelligence that reacts to indicators of compromise, ELLIO emphasizes proactive detection, providing security teams with early warning and actionable context to prevent incidents before they escalate.
Why does ELLIO focus on reconnaissance and mass exploitation?
These are the earliest phases of the attack lifecycle, where adversaries reveal intent before any damage occurs. By targeting threats upstream, ELLIO enables organizations to reduce operational burden, cut false positives, and stop attacks before they become costly.
Where is ELLIO based?
ELLIO is headquartered in Prague, serving organizations worldwide with real-time threat intelligence and security automation.

![[watchdog]: Inside a Mirai variant with six-layer persistence](/_astro/Mirai%20Botnet%20with%206%20layers%20of%20persistence%20Hero_Z2qvA8g.webp)












