
Threat intelligence on mass exploitation & recon activity for SOC workflows.
Gain real-time intelligence and context on mass exploitation and reconnaissance activity as it happens. ELLIO enriches and correlates security data to help identify and prioritize relevant threats over benign activity - reducing risk, cost, and SOC workload.
Reduce SIEM noise from mass automated traffic
Improve signal-to-noise ratio by filtering high-volume scanning, reconnaissance, and bot-driven traffic in real time. Isolate active malicious activity from background internet noise as it happens, improving alert quality, reducing false positives, and helping SOC analysts focus on what actually matters.
Stop repeat attacks behind rotating IP infrastructure
Correlate distributed reconnaissance and mass exploitation activity across changing IP addresses to detect persistent attacker campaigns, not just individual sources. Block behavior patterns instead of chasing single IPs.
Clean SIEM signals through perimeter-level intelligence
Combine perimeter defense and signal reduction in a single layer. Filter low-value and redundant traffic at the perimeter to improve alert quality in SOC workflows. Keep critical services explicitly allowed while blocking active malicious traffic at the first security layer, before it escalates into a costly incident.

Go beyond noise reduction.
ELLIO Threat Intelligence is designed for SOC-wide operational use, from human-led investigations to automated response workflows.
Context for human investigation & incident response
Data enrichment & automation for SIEM, SOAR, TIP, and other tools
Ground-truth metadata for AI agents & AI-assisted detection and analysis
Power automation with actor-level intelligence.
With ELLIO, you continuously enrich IP-based alerts linked to active mass exploitation and reconnaissance activity with the latest actionable context. Beyond basic IP classification, enriched intelligence includes:
Behavioral fingerprints
Identify scanning and exploitation tools even if the attacker rotates IPs.
Exploit history and CVEs
Map endpoints and payloads to real vulnerabilities.
Credentials and user agents
Track brute-force and login attempt patterns.
Historical activity timelines
See how targets, tactics, and tooling evolve over time.
MITRE ATT&CK mapping
Align with the MITRE ATT&CK framework to to correlate attack patterns.
Separate signal from background noise,
automatically.
ELLIO filters real reconnaissance and active mass exploitation from internet noise. It identifies scanners, AI scrapers, research crawlers, and botnets in real time, enabling your SIEM and SOAR to automatically deprioritize low-value alerts and focus on true risk.
Promiscuous mass internet scanners
AI/ML scraping tools
Opportunistic botnets
Benign research crawlers
Spray-and-pray campaigns
From global sensors to your security stack.
ELLIO Threat Intelligence flows from our global deception network through multiple channels, delivering actionable real-time insights directly into the security tools your team already uses.

[watchdog]: Inside a Mirai variant with six-layer persistence
An open directory is serving a Mirai variant across 14 CPU architectures - all updated yesterday. It kills competitors by SHA256 hash, persists through six layers, and hides as a kernel thread. Here's what's inside.

What Gets Deployed via Exposed Docker APIs
Over 1,000 unique IPs scan for exposed Docker APIs every day. A fraction go further. We captured every container creation payload and classified them by monetization strategy.
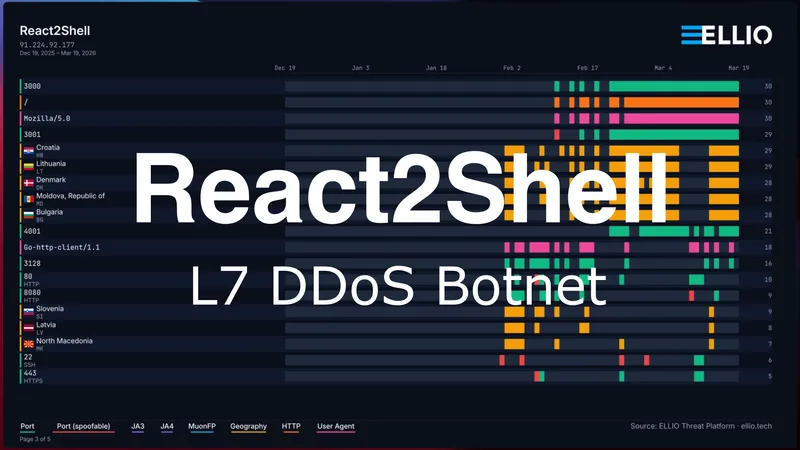
React2Shell Update: Custom Go L7 DDoS Botnet
A single delivery IP has been exploiting React2Shell to distribute malware from an open directory. 31 binaries including a custom Go L7 DDoS botnet with Cloudflare token forgery, two Mirai variants across 13 CPU architectures, and a C2 server.

![[watchdog]: Inside a Mirai variant with six-layer persistence](/_astro/Mirai%20Botnet%20with%206%20layers%20of%20persistence%20Hero_Z2qvA8g.webp)


