Exploitation and Reconnaissance Intelligence for SIEM & SOAR
ELLIO delivers real-time intelligence on who is connecting and why, so your SOC can separate targeted threats from internet noise, triage alerts faster, and automate response with confidence. Enrich alerts, deprioritize background activity, and track attackers across infrastructure changes directly inside your SIEM and SOAR.
Enrich Alerts
Go from raw IPs to fully classified and contextualized records. Instantly understand who is behind an alert and why it matters.
Reduce SIEM Noise
Separate background internet noise - scanners, crawlers, and opportunistic bots - from activity that signals real risk.
Automate Response
Feed real-time intelligence context directly into SOAR workflows so alerts can be routed, prioritized, and responded to automatically.
See what matters,
not just what’s malicious.
Traditional threat intelligence feeds tell you what’s malicious or binary IP reputation, leaving SOC teams to decide relevance. ELLIO goes further - tells you what it's doing right now and whether it's relevant to you.
| Traditional Agnostic Threat Intel | ELLIO Mass Exploitation and Reconnaissance Intel |
|---|---|
| Static IOC lists | Real-time behavioral classification from our global sensor network |
| Binary good/bad verdicts | Full context: source type, fingerprints, exploit history, and campaign activity |
| Noise reduction tools | Automatically tells you what to ignore and what to act on |
Understand who is behind every alert.
Every IP-based alert is enriched with intelligence from the global ELLIO Deception Network - including classification, behavioral fingerprints, exploit history, and campaign context - so your SOC begins triage with actionable answers, not questions. Key enrichment details that go beyond traditional IP classification include:
Behavioral fingerprints
Identify scanning and exploitation tools even if the attacker rotates IPs.
Exploit history and CVEs
Map endpoints and payloads to real vulnerabilities.
Credentials and user agents
Track brute-force and login attempt patterns.
Historical activity timelines
See how targets, tactics, and tooling evolve over time.
Separate signal from background noise - automatically.
ELLIO filters real reconnaissance and active mass exploitation from internet noise. It identifies scanners, AI scrapers, research crawlers, and botnets in real time, enabling your SIEM and SOAR to automatically deprioritize low-value alerts and focus on true risk.
Promiscuous mass internet scanners
AI/ML scraping tools
Opportunistic botnets
Spray-and-pray campaigns
Benign research crawlers
Automate with confidence.
Reduce manual investigation.
ELLIO delivers enriched context - classification, behavioral fingerprints, exploit history, campaign attribution, and more - before analysts even open a ticket. our SIEM and SOAR automatically prioritize alerts, run playbooks, and enforce blocking, letting analysts focus on high-priority threats, not noise.
Reduce analyst workload and alert fatigue
Accelerate SOC response time
Maintain automation accuracy
From global sensors to your security stack.
ELLIO Threat Intelligence flows from our global deception network through multiple channels, delivering actionable real-time insights directly into the security tools your team already uses.

Eliminate threats,
not just alerts.
Reduce operational burden and security spend by disrupting threats upstream, before incidents escalate. ELLIO intelligence strengthens your existing tools - firewalls, SIEM, SOAR, and TIP - by focusing on the earliest stages of the attack lifecycle: reconnaissance and mass exploitation, where adversaries reveal intent before impact.

Eliminate threats,
not just alerts.
Reduce operational burden and security spend by disrupting threats upstream, before incidents escalate. ELLIO intelligence strengthens your existing tools - firewalls, SIEM, SOAR, and TIP - by focusing on the earliest stages of the attack lifecycle: reconnaissance and mass exploitation, where adversaries reveal intent before impact.

[watchdog]: Inside a Mirai variant with six-layer persistence
An open directory is serving a Mirai variant across 14 CPU architectures - all updated yesterday. It kills competitors by SHA256 hash, persists through six layers, and hides as a kernel thread. Here's what's inside.

What Gets Deployed via Exposed Docker APIs
Over 1,000 unique IPs scan for exposed Docker APIs every day. A fraction go further. We captured every container creation payload and classified them by monetization strategy.
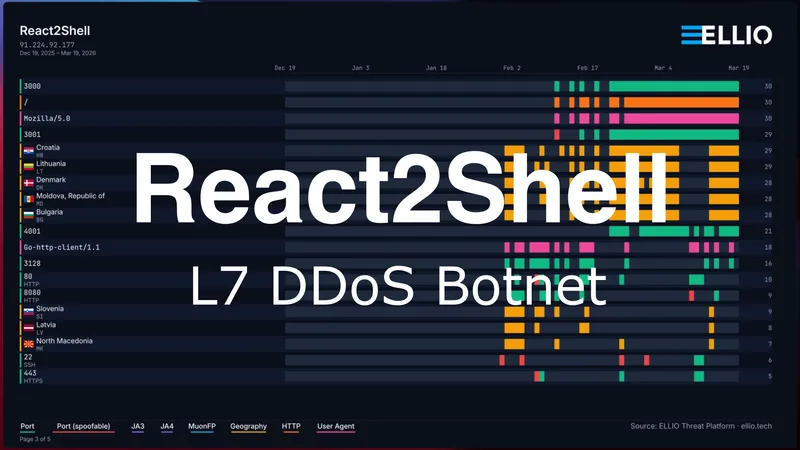
React2Shell Update: Custom Go L7 DDoS Botnet
A single delivery IP has been exploiting React2Shell to distribute malware from an open directory. 31 binaries including a custom Go L7 DDoS botnet with Cloudflare token forgery, two Mirai variants across 13 CPU architectures, and a C2 server.

![[watchdog]: Inside a Mirai variant with six-layer persistence](/_astro/Mirai%20Botnet%20with%206%20layers%20of%20persistence%20Hero_Z2qvA8g.webp)

