Posts by
ELLIO Threat Research Lab

[watchdog]: Inside a Mirai variant with six-layer persistence
An open directory is serving a Mirai variant across 14 CPU architectures - all updated yesterday. It kills competitors by SHA256 hash, persists through six layers, and hides as a kernel thread. Here's what's inside.

What Gets Deployed via Exposed Docker APIs
Over 1,000 unique IPs scan for exposed Docker APIs every day. A fraction go further. We captured every container creation payload and classified them by monetization strategy.
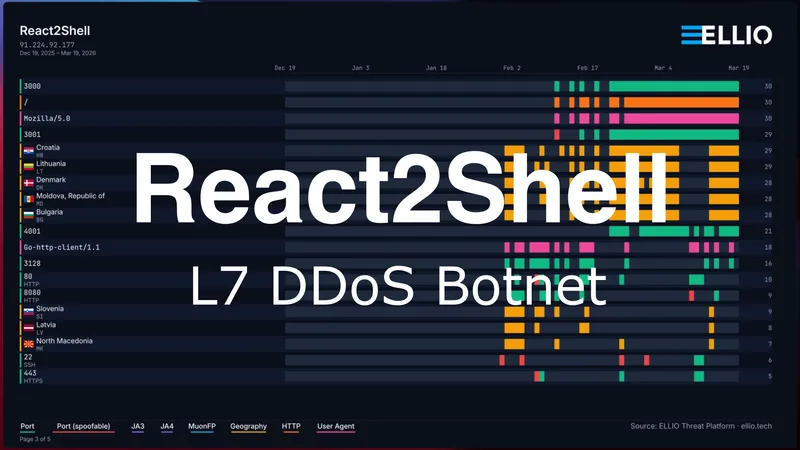
React2Shell Update: Custom Go L7 DDoS Botnet
A single delivery IP has been exploiting React2Shell to distribute malware from an open directory. 31 binaries including a custom Go L7 DDoS botnet with Cloudflare token forgery, two Mirai variants across 13 CPU architectures, and a C2 server.
_Z2vxzLx.webp)
Coordinated Credential-Stuffing Campaign Targets Palo Alto GlobalProtect Portals
A coordinated credential-stuffing campaign hit GlobalProtect VPN portals with 8,575 IPs in 48 hours. Three attack waves, 78 targeted usernames, one password. Our team breaks down the timeline, infrastructure, fingerprints, and what defenders can do.

React2Shell in the Wild: Payload Analysis, Active Campaigns, and IoCs
The ELLIO sensor network has been tracking active exploitation of CVE-2025-55182 (React2Shell) in the wild. Here’s what we’re seeing.

From Scan to Exploit: Inside the Latest Cisco ASA/FTD Campaign
From reconnaissance to exploitation in just 48 hours. See how 75 IPs executed surgical, one-hit attacks on Cisco ASA/FTD devices - and how to disappear from target lists.
Every packet tells a story: The evolution of fingerprinting and netsec
The journey began in 1969, when the very first RFC - Request for Comments - was published. Explore key milestones that shaped network security and the practice of network fingerprinting.
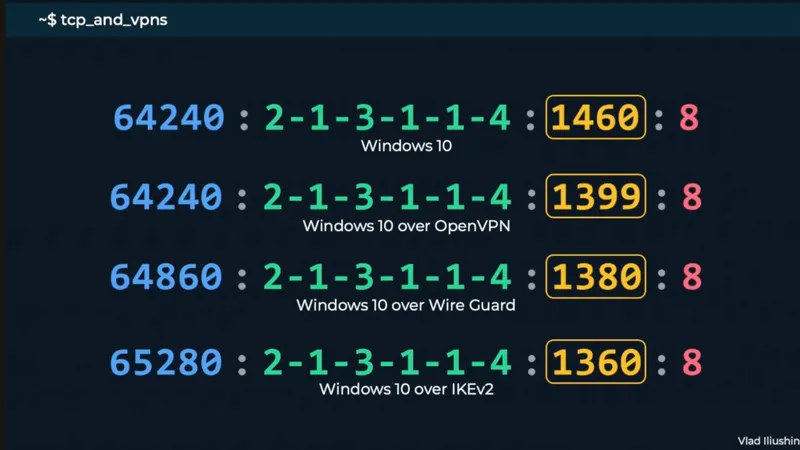
Video: How to capture real value from network fingerprinting in practice
Learn practical tips for deploying JA4, JA3, and MuonFP fingerprints in your security operations. Get expert insights from Vlad Iliushin and discover how to unlock their full defensive value.
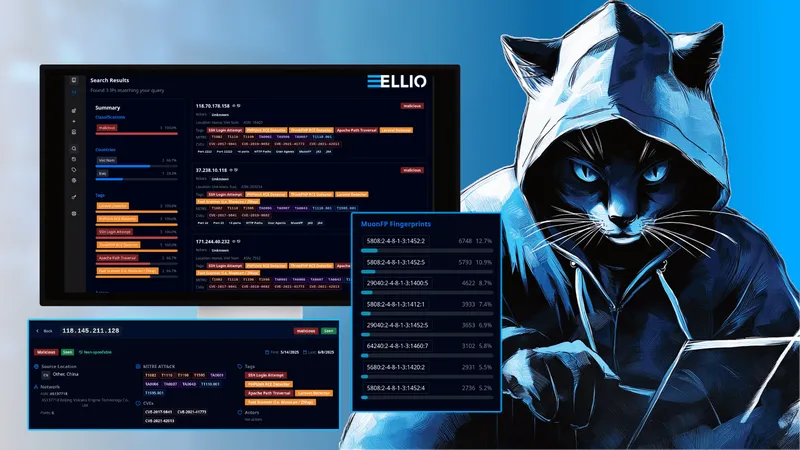
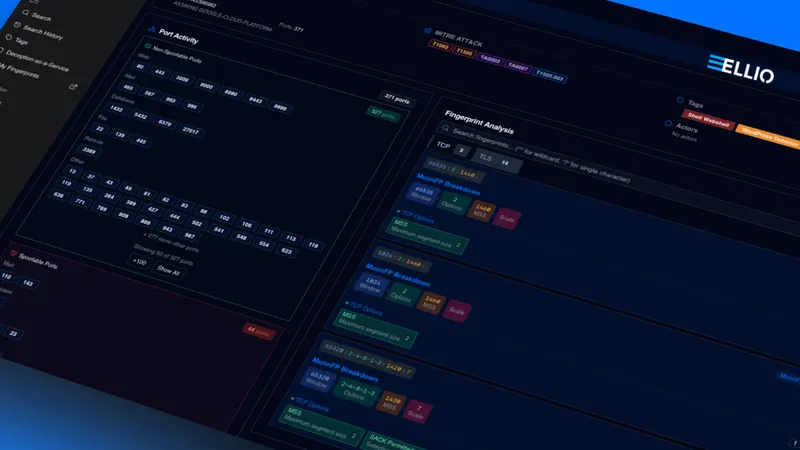
MITRE ATT&CK® framework now integrated into ELLIO Threat Platform
Transform your threat investigations with the ELLIO Threat Intelligence Platform. Now with MITRE ATT&CK threat mapping and advanced fingerprint analysis.