Analyze everything or move straight to network-level blocking?
One IP. Four days. Nearly 900 user agents. Over 3,000 probes. Sometimes a single IP address tells you everything you need to know about how industrialized internet scanning has become.
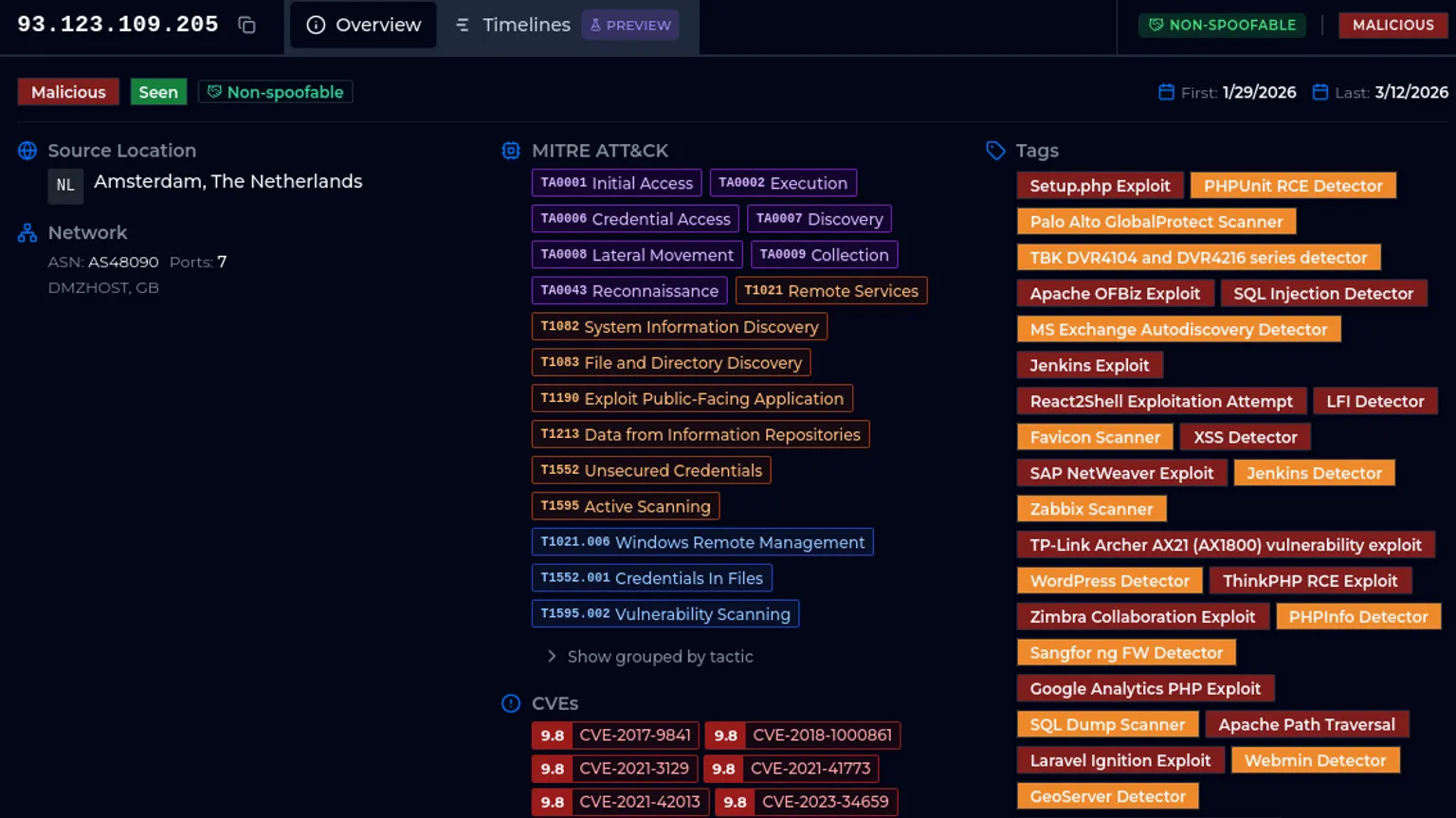
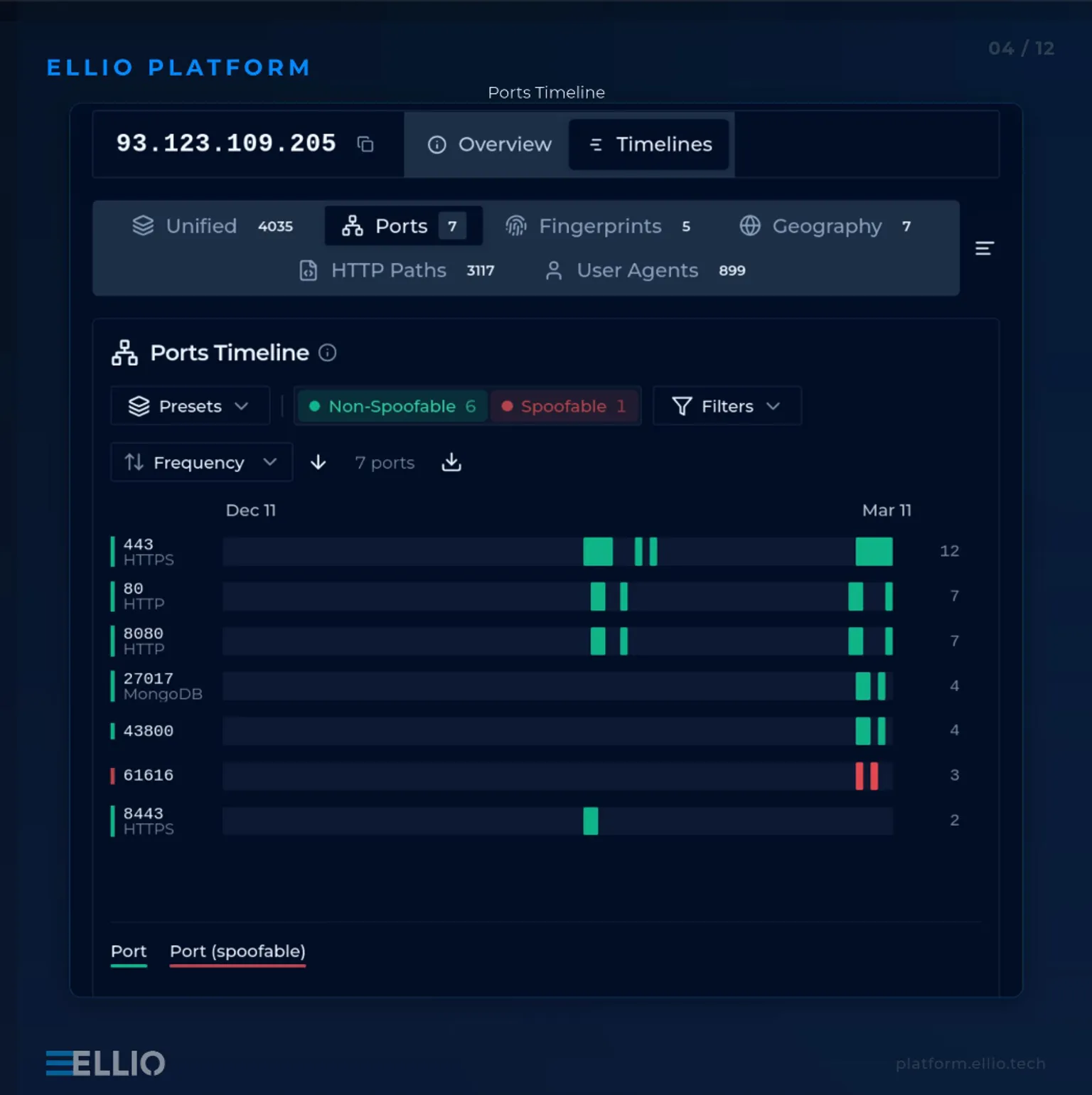
Between March 6–12, a single IP address 93.123.109.205, hosted on DMZHOST in Amsterdam, lit up ELLIO Honeypot Network. What followed was a scanning spree:
• 37 detection signatures triggered
• 3,117 unique HTTP paths probed
• 899 distinct user-agent strings observed
• 7 different ports targeted
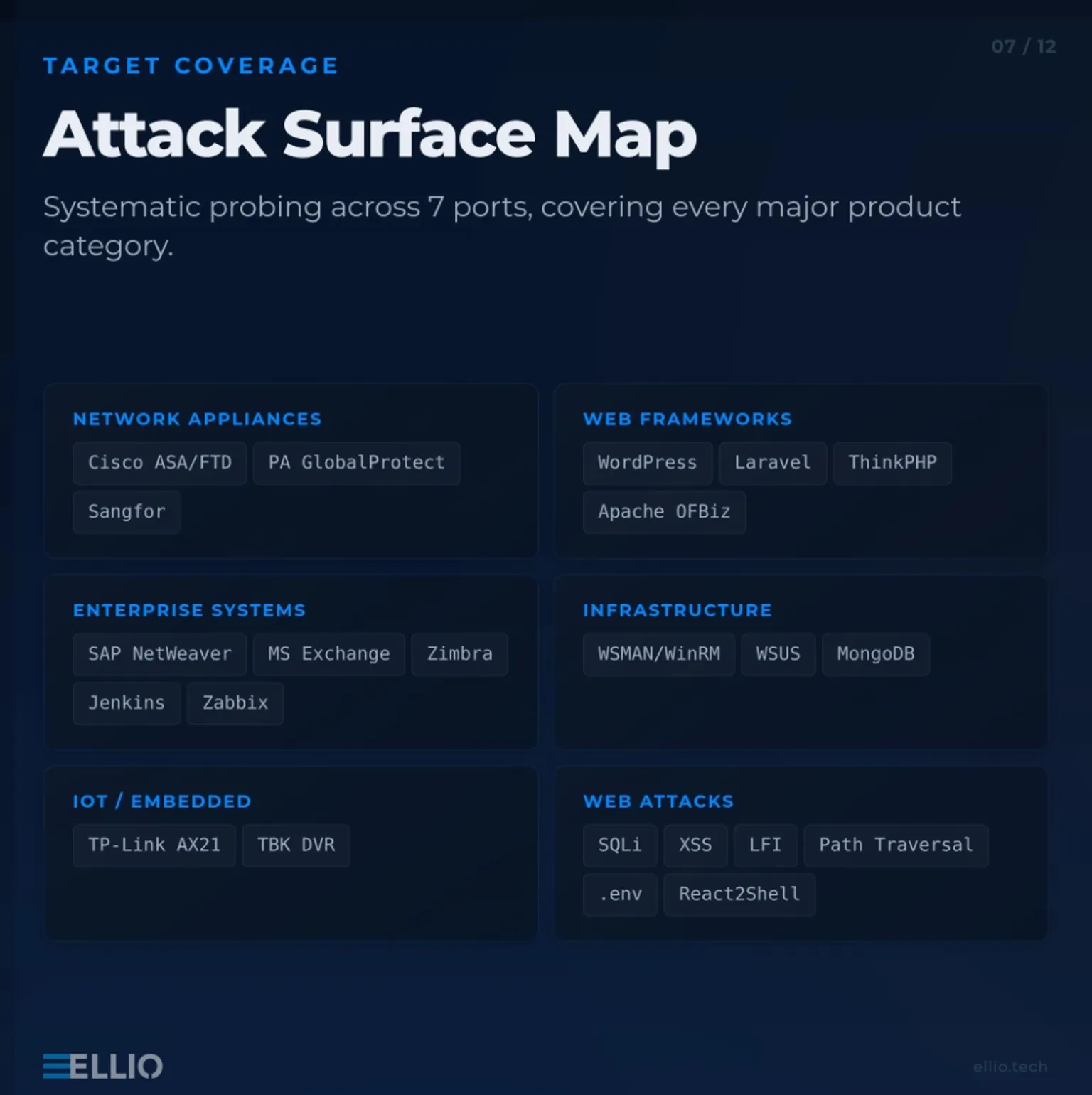
The activity included 16 exploit signatures and 21 reconnaissance/scanner signatures, touching a surprisingly wide attack surface:
Network appliances
• Cisco ASA / FTD
• Palo Alto GlobalProtect
• Sangfor
• SonicWall
Web frameworks
• WordPress
• Laravel
• ThinkPHP
• Apache OFBiz
• Jenkins
Enterprise platforms
• SAP NetWeaver
• Microsoft Exchange
• Zimbra
• Zabbix
Infrastructure targets
• Docker
• WSMAN / WinRM
• WSUS (CVE-2025-59287)
IoT / embedded devices
• TP-Link Archer AX21
• TBK DVR
• D-Link
Plus the usual web exploitation attempts:
SQL injection, XSS, LFI, path traversal, .env harvesting, and React2Shell.

Even the user-agent strings were unusual.
Among the 899 unique UAs, we saw fabricated OS identifiers like:
“CentOS Chrome 134.0”
“Fedora Chrome 137.0”
Some even contained embedded Shellshock payloads.
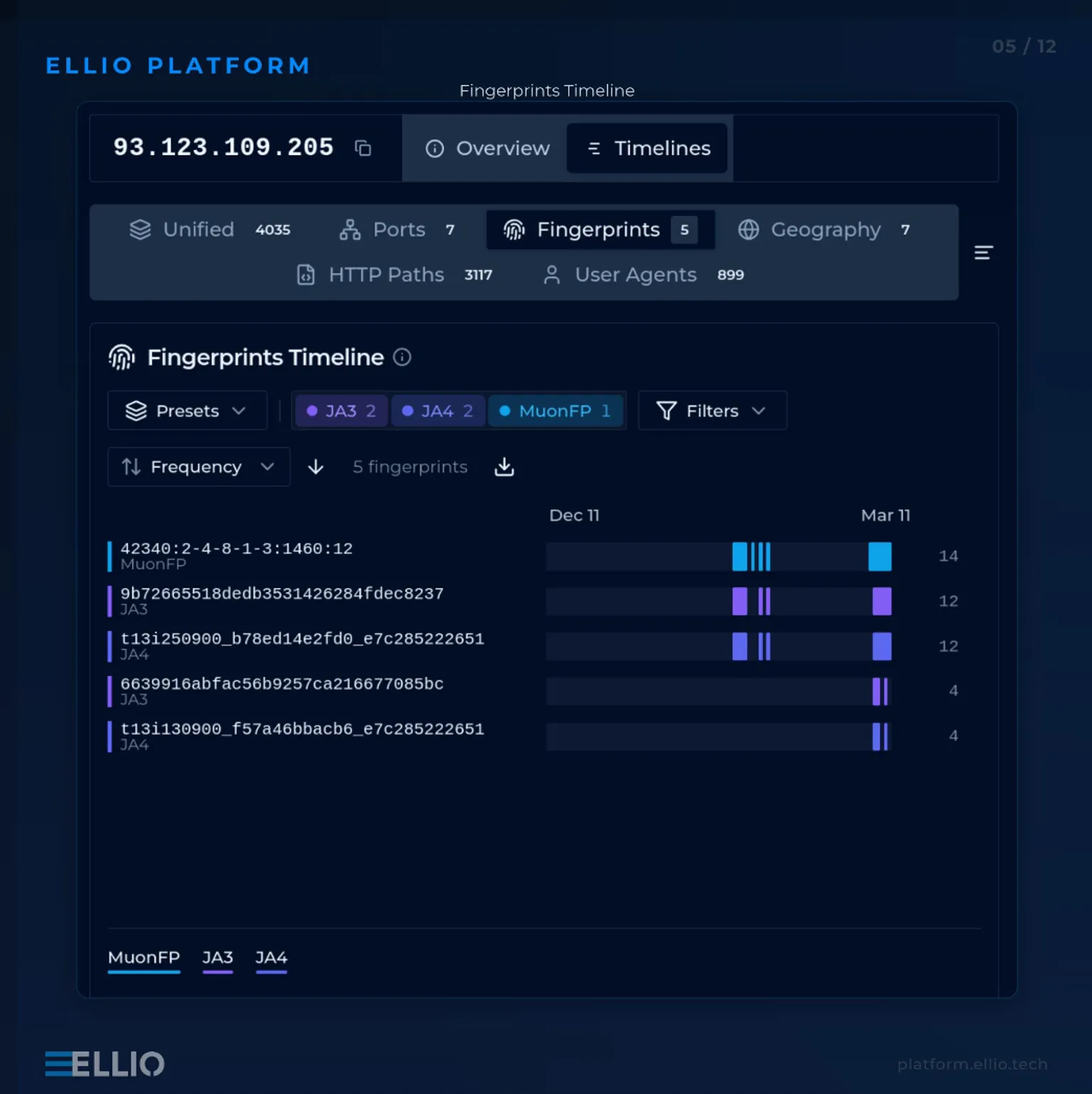
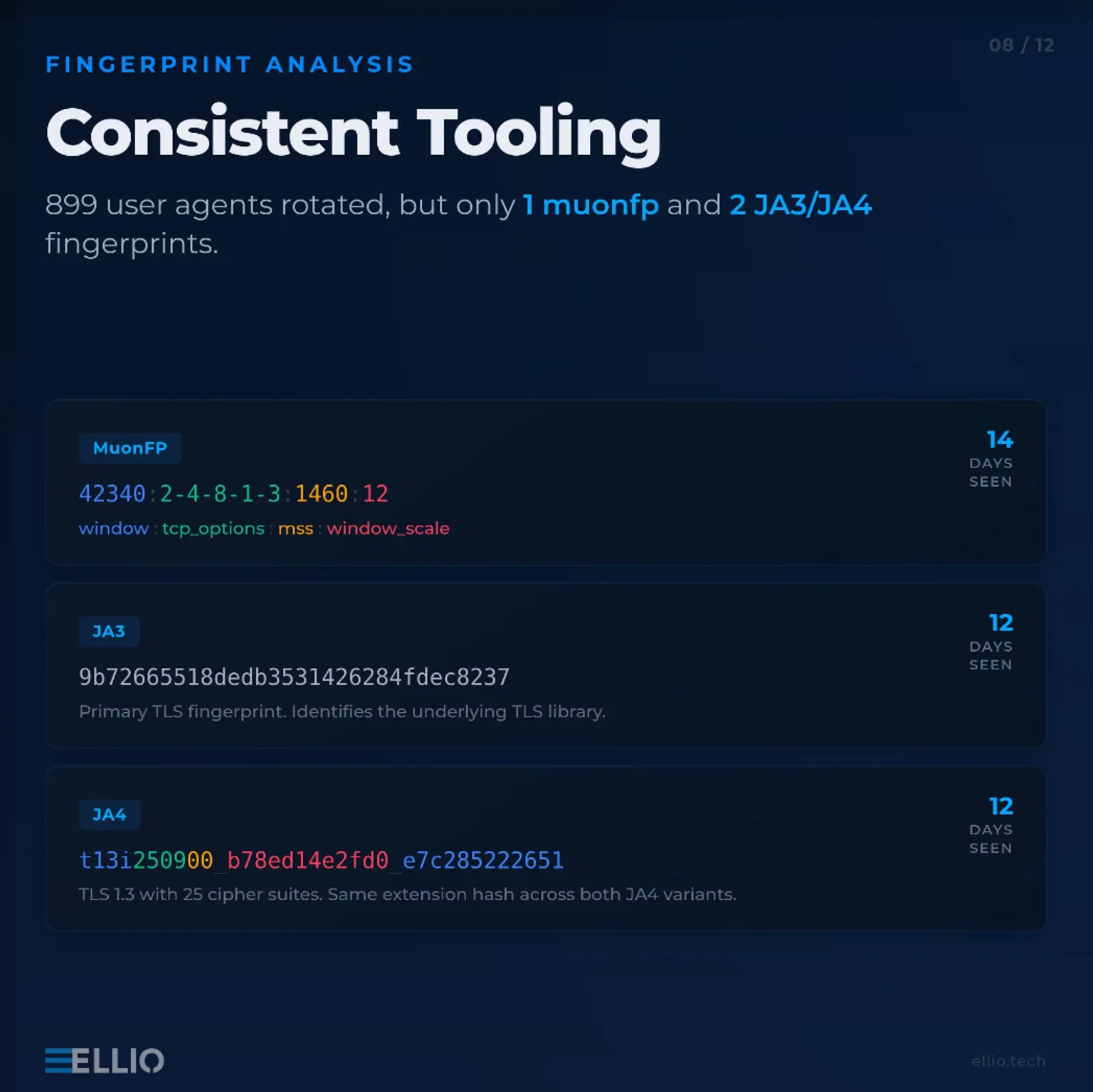
At the fingerprinting level, the activity was highly consistent:
• MuonFP: 42340:2-4-8-1-3:1460:12
• Two JA3 hashes
• Two JA4 hashes
• All connections classified as non-spoofable
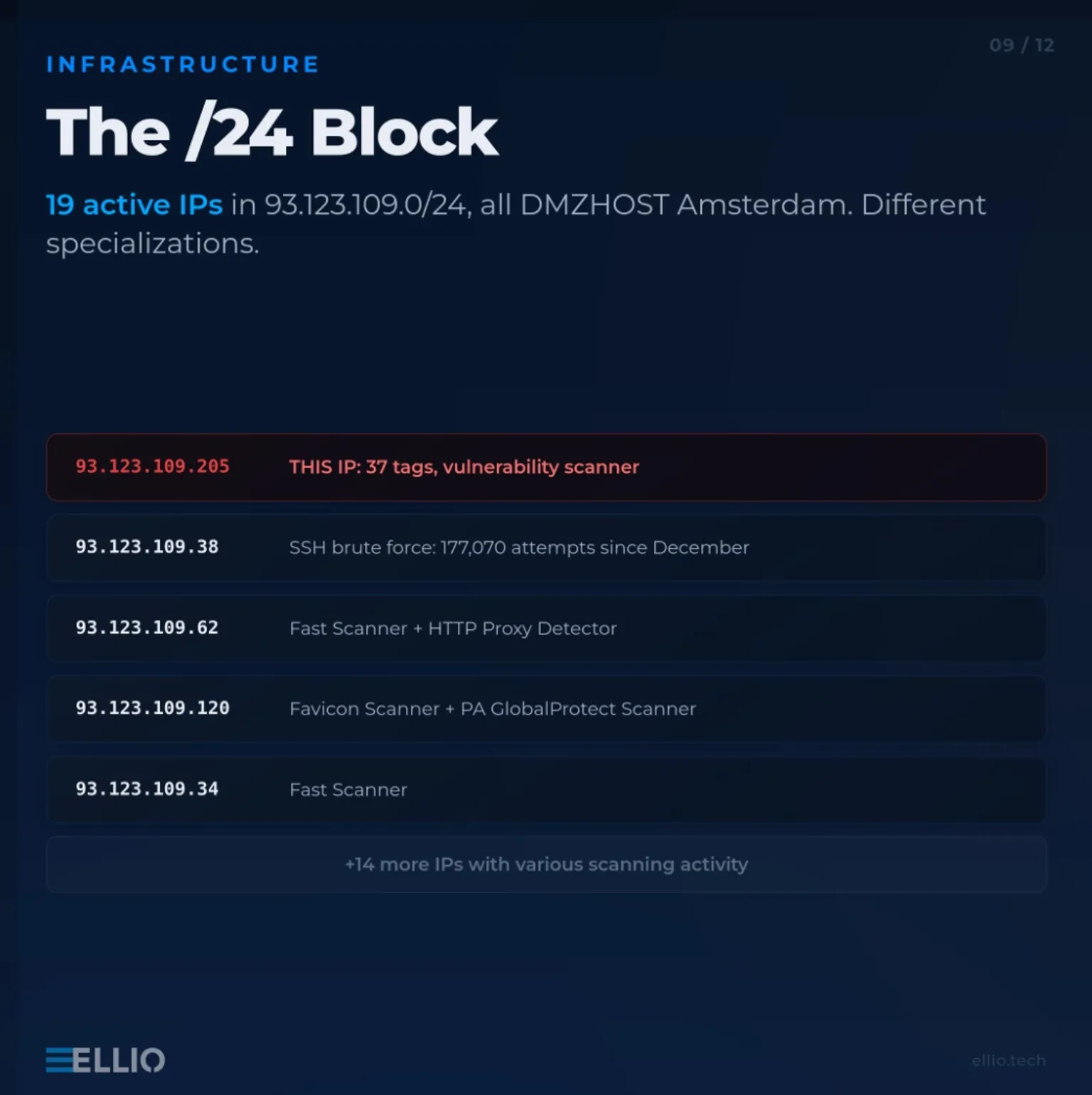
Looking deeper at the infrastructure reveals a familiar pattern.
The hosting provider’s corporate footprint has cycled through multiple shell companies, all registered at the same London virtual office:
35 Firs Avenue, London N11 3NE
• Pre-2016 — Dmzhost Limited (Seychelles)
• 2016–2018 — Jupiter 25 Limited (UK)
• 2019–2024 — PPTECHNOLOGY LIMITED (UK)
• 2024–present — TECHOFF SRV LIMITED (UK) (current RIPE registrant for AS48090)
Four entities. One address. Continuous operation.
And this isn’t new.
This infrastructure has shown persistent scanning activity for nearly a decade, with the same patterns appearing repeatedly from the surrounding IP ranges.
At some point, the conclusion becomes obvious.
When activity originates from long-standing bulletproof hosting infrastructure, spending hours analyzing individual exploit attempts isn’t the best use of a defender’s time.
Sometimes the most efficient response is simply:
Block the IP range.
And focus your investigation effort on threats that actually require it.
How does your team handle abuse from persistent scanning infrastructure like this?
Do you analyze everything or move straight to network-level blocking?
Written by

A team of passionate brand evangelists at ELLIO, connecting and supporting the cybersecurity community through events, knowledge sharing, and collaboration.
Read next
All posts →
IP Blocking vs TCP Fingerprint Blocking: How to Use and Combine Them
Learn how combining Threat Intelligence-based IP blocking and TCP fingerprinting enhances network security by disrupting attacker reconnaissance.


From Scan to Exploit: Inside the Latest Cisco ASA/FTD Campaign
From reconnaissance to exploitation in just 48 hours. See how 75 IPs executed surgical, one-hit attacks on Cisco ASA/FTD devices - and how to disappear from target lists.
_Z2vxzLx.webp)
Coordinated Credential-Stuffing Campaign Targets Palo Alto GlobalProtect Portals
A coordinated credential-stuffing campaign hit GlobalProtect VPN portals with 8,575 IPs in 48 hours. Three attack waves, 78 targeted usernames, one password. Our team breaks down the timeline, infrastructure, fingerprints, and what defenders can do.