Recon & Mass Exploitation Research
Threat research on reconnaissance and mass exploitation activity from ELLIO. Read the latest threat news and defense analysis.
Page 2 of 3

From Scan to Exploit: Inside the Latest Cisco ASA/FTD Campaign
From reconnaissance to exploitation in just 48 hours. See how 75 IPs executed surgical, one-hit attacks on Cisco ASA/FTD devices - and how to disappear from target lists.
Every packet tells a story: The evolution of fingerprinting and netsec
The journey began in 1969, when the very first RFC - Request for Comments - was published. Explore key milestones that shaped network security and the practice of network fingerprinting.
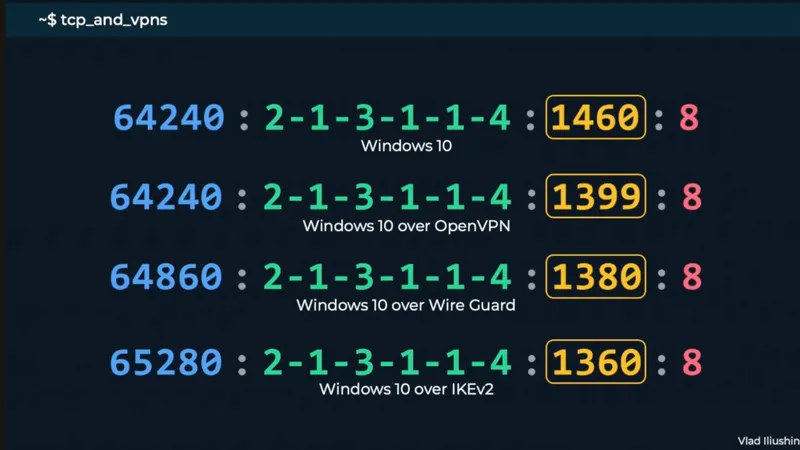
Video: How to capture real value from network fingerprinting in practice
Learn practical tips for deploying JA4, JA3, and MuonFP fingerprints in your security operations. Get expert insights from Vlad Iliushin and discover how to unlock their full defensive value.
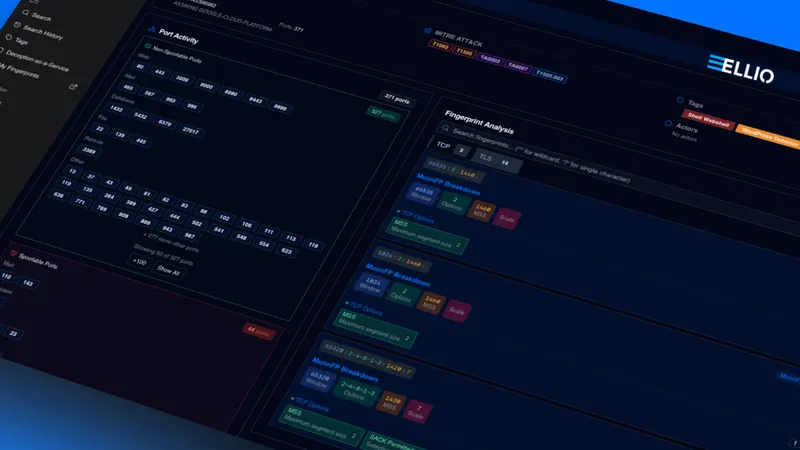
MITRE ATT&CK® framework now integrated into ELLIO Threat Platform
Transform your threat investigations with the ELLIO Threat Intelligence Platform. Now with MITRE ATT&CK threat mapping and advanced fingerprint analysis.

IP Blockling on FortiGate 7.2.0/7.4.0 using ELLIO
This article gives you a simple, step-by-step guide to set up an external IP blocklist and firewall rules on FortiGate 7.2.0/7.4.0. Discover why adding advanced ELLIO Blocklists to your FortiGate v. 7.2.0/7.4.0 is a great way to boost its protection, and how easy it is to set up.

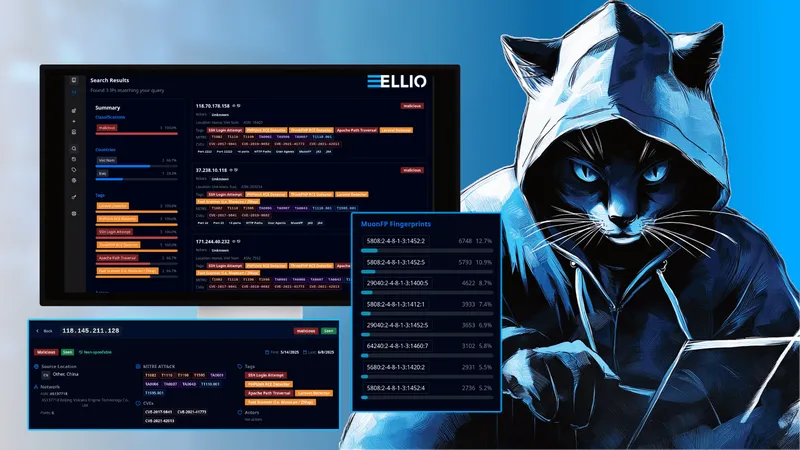
IP Blocking vs TCP Fingerprint Blocking: How to Use and Combine Them
Learn how combining Threat Intelligence-based IP blocking and TCP fingerprinting enhances network security by disrupting attacker reconnaissance.

Managing blocklists using a central platform (part 3)
Learn how SOCs, NOCs and MSSPs are leveraging centralized blocklist management to reduce false positives and simplify security management.
Managing blocklists using a central platform (part 2)
Explore 8 essential steps for building and deploying effective IP blocklists with the Blocklist Management Platform.
Managing blocklists using a central platform (part 1)
Learn how blocklist management platforms empower SOCs and NOCs. Streamline processes, minimize errors, and enhance network security.